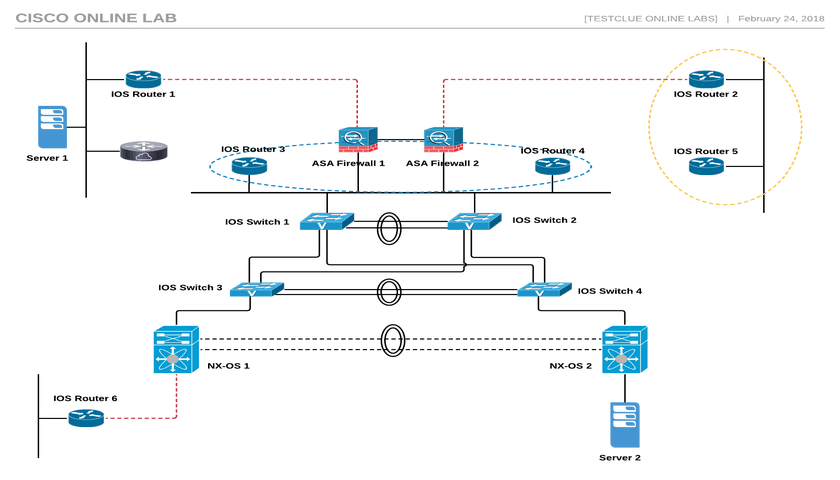
This Cisco online lab consists of 17x virtual appliances, with combination of NX-OS, ASA FWs, Cisco routers and switches. It also includes 2x small servers for testing end-to-end configuration and topology. On this page you will find useful information about the lab devices, links, useful tutorials and troubleshooting information. This network is based on VIRL and built on machine providing 8 vCPUs, 21 GB RAM and 200 GB of HDD Storage.
Cisco Online Lab Setup
- Total 17 nodes are possible in different configurations (please refer to List of Devices section below)
- You can choose to use the existing topology or design your own for practice.
- Possibility of accessing lab devices natively via SSH / Putty once configured.
- Access to browser based console sessions to configure devices.
- Ready topology diagram is the one shown on this page and can also be downloaded.
- You can create new layer 2 vlans and layer 3 interfaces, networks on devices, 192.168.80.x IPs are used for mgmt
- Please do not use 192.168.80.0/24, 192.168.100.0/24 and 10.255.0.0/24 networks in configuration
- You can save config on lab desktop and email to yourself for later use
LAN Servers :
- Two ubuntu servers are also provided in topology
- Login to both servers : cisco / cisco
- These are ubuntu machines, can be used for end-to-end testing of network.
- IP address of server is available in Device IP Addressing list below
- These servers are accessible only via web console
List of Devices :
- 6x Cisco IOSv Routers
- 4x Cisco IOSvL2 Switches
- 2x Cisco ASA Firewalls in HA mode
- 2x NX-OS Appliances
- 2x Ubuntu Servers for Application Testing
- 1x Windows 7 PC for Configuration
Lab Information and Instructions :
If you have booked server time already please login to Lab Console below, credentials delivered via email used during booking. For booking new time slot, click here.
- connect via above link, login with emailed user/pass
- second level of authentication, will be sent via email
- list of devices available to connect – Windows pc, Cisco Devices
- connect to Windows 7 pc from listed connections, connect as – labuser / Labroot12!@
- Cisco device Login – cisco/cisco
- Lab will be auto-destroyed after 10 minutes from end of session
- All lab devices will be accessible via browser based console / CLI access
- *To enable SSH access to a device from internet, please add a default or specific route (to your public IP) pointing to 192.168.80.1
*for example if you want to access lab devices directly via ssh from your personal PC, and your internet IP address is 1.2.3.4 then add this route on cisco devices : ip route 1.2.3.4 255.255.255.255 192.168.80.1
Device IP Addressing and SSH Ports (available once default route added from CLI console access)
| Public IP | SSH Access Port | Cisco Device IP | Device Type |
| 77.93.215.14 | 2001 | Not Available | None |
| 77.93.215.14 | 2002 | Not Available | LXC |
| 77.93.215.14 | 2003 | 192.168.80.241 | ASA 1 |
| 77.93.215.14 | 2004 | 192.168.80.242 | ASA 2 |
| 77.93.215.14 | 2005 | 192.168.80.243 | CSR |
| 77.93.215.14 | 2006 | 192.168.80.244 | Router 1 |
| 77.93.215.14 | 2007 | 192.168.80.245 | Router 2 |
| 77.93.215.14 | 2008 | 192.168.80.246 | Router 3 |
| 77.93.215.14 | 2009 | 192.168.80.247 | Router 4 |
| 77.93.215.14 | 2010 | 192.168.80.248 | Router 5 |
| 77.93.215.14 | 2011 | 192.168.80.249 | Router 6 |
| 77.93.215.14 | 2012 | 192.168.80.250 | Switch 1 |
| 77.93.215.14 | 2013 | 192.168.80.251 | Switch 2 |
| 77.93.215.14 | 2014 | 192.168.80.252 | Switch 3 |
| 77.93.215.14 | 2015 | 192.168.80.253 | Switch 4 |
| 77.93.215.14 | 2016 | 192.168.80.221 | NX-OS 1 |
| 77.93.215.14 | 2017 | 192.168.80.222 | NX-OS 2 |
| None | NA | 192.168.80.223 | Ubuntu 1 |
| None | NA | 192.168.80.224 | Ubuntu 2 |
Useful Links :
For Troubleshooting and technical discussion please use this forum :
Issues During Lab Session
- Please use live chat option on bottom right of this page. (In case no response within 5 mins, please use option below)
- Red “Technical Support” button on top right hand corner of page is provided to open tickets and advance support.
Looking for something?
Upcoming Webinars
Tags
african virtual university
alignment
audio
Authentication
captions
cassandra
Cassandra Authentication
Codex
comments
content
css
database
database access control
distance learning
edge case
electrical engineering jobs
embeds
excerpt
F5 Lab Guide
featured image
formatting
gallery
html
image
indexing
lists
LTM Lab Guide
markup
mongodb
MongoDB Compaction
nsx
nsx controller
nsx manager
online education
online learning
post
Post Formats
read more
shortcode
standard
technical education
template
title
video
vmware